As 2025 winds down and major industry events wrap up, conversations start circling the same question: what will next year bring for mobile security?
Budgets are being approved, product roadmaps finalized, and the stakeholders are trying to predict the next cybercrime evolution and how to ensure they can stay protected.
Reality check? The mobile threat landscape is changing faster than most organizations can respond to, and the stakes seem to never have been higher.
Recent industry research shows that AI turned out to be a major catalyst for social engineering. Moverover, attackers seem to be focused on breaching identities while credential theft remains the most common way to breach an organization. At the same time, companies are increasing their mobile security budgets, SIM swapping keeps rising, and there seems to be a push to remove users from the process of authentication.
I’ve had a look at some of the recent cybersecurity reports and managed to break down five key trends every telco and mobile app developer should understand, along with practical tips on addressing them right away.
1. AI Supercharges Social Engineering and Impersonation Attacks
Having warmed up in 2024 and 2025, it seems that 2026 is shaping up to be the full arrival of AI-driven cybercrime.
Since attackers don’t need to spend time writing convincing phishing messages themselves, social engineering attacks receive a boost at scale. With Gen AI, attackers can craft highly tailored, sophisticated phishing emails, SMS messages or even voice prompts in seconds. And the stats prove this.
According to recent findings from Microsoft, AI-powered phishing emails achieved a 54% click-through rate, compared to 12% for standard phishing attempts. The same report noted that 57% of organizations saw an increase in security incidents linked directly to AI tools.
Verizon’s data reinforces this trend, showing that nearly 60% of breaches still involve a human element, illustrating just how effective AI-generated social engineering is. What’s more, we’ll likely never be able to completely prevent it unless we change our approach to authentication.
The crux of the matter is this: most login flows still depend on user behaviour.
If a user can be tricked into typing a password, sharing a one-time code, or approving a prompt, then even the most secure infrastructure becomes irrelevant. With AI, this human weakness grows even bigger because the messages are increasingly indistinguishable from legitimate communication.
As these attacks grow more sophisticated, the safest authentication methods will be those that minimize user involvement and rely on independent signals that cannot be phished or impersonated.
2. Mobile Credential Theft Explodes as Identity Becomes the Primary Attack Surface
Across the industry, identity has emerged as the primary attack surface for attackers, leaving traditional defenses struggling to keep up.
According to Verizon, stolen credentials were the most common initial access vector this year, accounting for 22% of all breaches. Microsoft’s recent findings point in the same direction, reporting a 32% rise in identity-based attacks in the first half of 2025 alone.
A major driver of this shift is the ongoing decline in password quality.
NordPass revealed that at least 42% of the world’s top 1,000 websites still allow weak password rules, and attackers take full advantage. Predictable, reused, or weak passwords continue to open the door for account takeover.
The now well-known Louvre example, where employees used the password “Louvre” inside their systems, may sound extreme, but it reflects a much broader pattern. Weak credentials remain one of the easiest paths into an organization.
With the same goal, infostealer attacks have gone fully mainstream.
A 2025 report found that infostealer attacks surged by 58% year over year. Moreover, IBM’s X-Force team uncovered a similar trend, reporting that in 2024 there were, on average, 84% more infostealers delivered via phishing emails each week than in 2023. Early 2025 data suggested an even sharper rise, with weekly distribution up by as much as 180% compared to 2023.
In recent years, mobile devices have become the primary gateways to both personal and business applications, and as such, they store more sensitive data than ever before.
Any authentication method that relies on user-entered information, locally stored tokens, or SMS codes becomes increasingly vulnerable to both poor password hygiene and infostealer activity.
This is why more organizations are shifting toward passwordless authentication. Not only are these methods seamless and don’t frustrate the user, but they help nip this problem in the bud.
With no weak password for the user to set, or for the attacker to steal, it’s a great decision for 2026.
3. SIM-Swapping Surges, Forcing a Rethink of Phone-Number Security
In 2025, SIM swapping kept climbing the list of most popular cybercrime strategies.
For example, in the UK, the number of unauthorized SIM-swap cases surged 1,055% in 2024, from 289 in 2023 to nearly 3,000 documented incidents. That dramatic jump turned phone number hijacking into one of the fastest-growing fraud vectors in the mobile ecosystem.
When an attacker successfully SIM swaps, they can bypass SMS-based 2FA, intercept recovery flows, and take over accounts fairly easily. And because SMS 2FA is still widely used, large user bases are left vulnerable.
However, more than just a problem to users, this increase in SIM swapping is a signal for telcos and mobile app developers that it may be time to retire SMS OTPs.
Some of them have successfully decoded this signal with banks in Malaysia, Hong Kong, and UAE banning this authentication method and turning to device-based authentication.
On the other hand, we also have SIM Swap Detection solutions, including our very own.
Upon detecting a new SIM card, IPification SIM Swap Detection sends a real-time notification to the mobile app developers, and gives them the power to stop any authentication requests until the user confirms they’re indeed using a new SIM card, thus preventing any damage from being done. Nifty!
4. Mobile Security Budgets Rise as Cybercrime Accelerates
With cybercrime climbing year after year, it’s no surprise that organizations are putting more money into mobile security.
Verizon reports that 75% of companies increased their mobile security spending in the past twelve months, and the increase in mobile-focused attacks, from credential theft to SIM swapping fraud, helps illustrate why this is happening.
Most of this investment is going toward strengthening mobile device management, mobile identity improvements, and tightening compliance requirements. For many companies, these areas were overdue for attention as mobile devices became the primary way employees and customers access critical services.
It also raises a useful question: has your organization made the same move?
This increase in investment is a positive shift for the industry as a whole, and as mobile apps take on more sensitive data and attackers continue to target mobile ecosystems, staying ahead of the curve will only become more important.
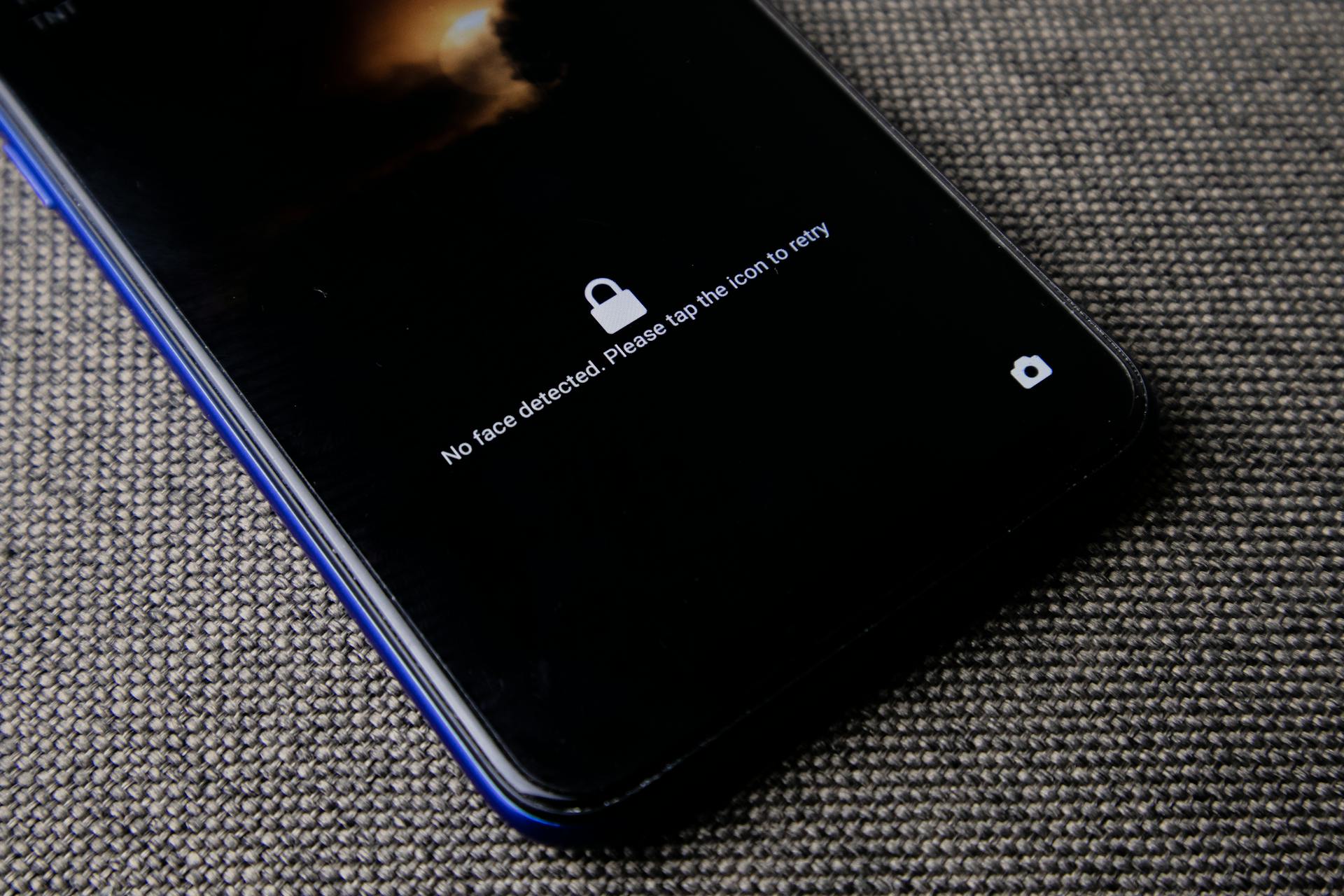
5. The Push to Remove Users From Authentication Gains Momentum
As we head into 2026, it seems that the move to remove the user from the authentication process is gaining momentum globally.
After years of constantly changing recommendations and an overload of login rules, users are simply burned out, and the industry is realizing that no amount of advice or education will ever fully fix human error.
For years, users were told to create long, complex passwords and change them regularly.
Then NIST updated its guidelines, noting that frequent forced password changes actually make security worse because people resort to predictable variations.
Password managers were supposed to help, and they do in theory, but in practice the experience is often frustrating. Having to type in a long and complex master password every time you want to autofill a login leads many people to abandon the process entirely.
Combine that with juggling dozens or even hundreds of accounts, and the result is inevitable: shortcuts. People reuse passwords, slightly modify old ones, or choose something easy enough to remember at the expense of security.
Factor in social engineering such as phishing, fake prompts, impersonation, etc, and it becomes clear that no amount of training or policy changes can eliminate the human element entirely. As long as authentication depends on what users choose, type, or confirm, the system will always have cracks.
How to Prepare for 2026
Taken together, these trends point in the same direction: mobile security is entering a new phase where traditional defenses simply can’t keep up.
AI is reshaping social engineering at scale, credentials remain the easiest way into an organization, SIM swapping continues to rise, companies are investing more in mobile protection, and users are overwhelmed by authentication methods that place too much responsibility on them.
If 2025 taught us anything, it’s that 2026 will demand approaches that reduce user friction, minimize human error, and rely on stronger mobile authentication than passwords or SMS codes.
This is the direction IPification was built for, to help organizations future-proof their mobile security systems. Instead of depending on user input, IPification uses a combination of device, SIM card, and mobile network data to authenticate users seamlessly. It removes the risky touchpoints that attackers target, while keeping the experience fast and invisible to the user.
In a world where AI-generated phishing messages look indistinguishable from legitimate communication, methods that rely on users to spot manipulation are becoming increasingly unreliable. By eliminating passwords and one-time codes entirely, IPification removes the very element attackers depend on. Even malware designed to steal credentials or authentication cookies loses most of its power when there is no password to capture or token to replay. And when it comes to SIM swapping, IPification’s real-time detection notifies service providers the moment a SIM change occurs, giving them the ability to pause authentication until the legitimate user confirms the activity.
As mobile security budgets continue to grow, companies are looking for solutions that will keep them ahead of attackers, not just react to them. And as users grow increasingly fatigued with complex login rules, password managers, master passwords, and constant prompts, authentication must become simpler, not harder.
As 2026 approaches, the organizations that thrive will be the ones that shift toward secure, seamless, and private authentication methods, and this is the exact trifecta on which we’ve based IPification.
Every app has different needs, and if you’re unsure whether IPification is the right approach, we’d be happy to help you evaluate your options. Reach out to schedule a free consultation with our team and discover the best direction for your mobile security strategy.