By Statista, an average smartphone user is daily spending more than 5h on the device as we do not just use it to communicate, but also to watch TV, listen to the music, play games, and, more importantly, buy and make different transactions online.
Since we know that almost 5 billion people are using smartphones daily for the purposes mentioned, it is clear that security needs to be on the highest level possible.
This user behavior is the reason why mobile authentication solutions are becoming so important in securing the mobile identity and personal data.
Alongside simple usernames and passwords, the most commonly used authentication methods now are 2-Factor Authentication options (2FA), or Multiple Authentication options (MFA). They are designed to strengthen user security by adding an additional factor to the already existing username-password combination.
There are multiple options available but the most widely used are 2FA options harnessing the mobile operator’s communication channels and technologies like SMS/ Voice,and most recent, header enrichment. They are gaining different traction in usability and market potential as they are all trying their best to balance between 3 main elements – security, user experience, and privacy.
For the sake of a valuable comparison, we have analyzed all of these 3 elements for the most widely used 2FA methods and compared it to IPification – a new generation, mobile authentication method created by our team.
SMS One Time Password (OTPs) – poor security and deprecated authentication solution?
OTPs via SMS has been around for a long time. Their market penetration is high so the average user is familiar with a not that smooth experience. Alongside the not that smooth experience, it has been proven so many times as an insecure method for user authentication.
SS7 technical flaws within the mobile network can be exploited for interception and rerouting of an SMS message containing an OTP. Or a hacker can use malware on the user’s phone to forward the SMS. Recent Reddit breach proves that SMS as a 2FA channel cannot be trusted and that these type of threats are very alarming – they are scalable and can occur remotely.
The issue with SMS as 2FA channel has been recognized by US standards-setting agency NIST back in 2016, stating that SMS authentication is a deprecated authentication method. We couldn’t agree more.
If we forget about security and the user experience for a second, we come to the very important question of user privacy. Is SMS 2FA using any of your personal data for authentication? Of course – it’s your mobile phone number which needs to be stored on the company’s server to simplify the authentication process. Taking all of this into consideration, OTPs via SMS will not be around for much longer.
HTTP Header Enrichment – smooth user experience with low security
There are many new companies growing their market traction and building their stories on solving at least one of the issues that SMS as 2FA has – user experience. Most of these “new” and “revolutionary solutions” are actually harnessing an old mobile network technology – HTTP header enrichment.
It is true that header enrichment used in 2FA authentication process gives an extraordinary user experience – it is automatic and does not require any action from the user to complete the authentication process.
The issue with header enrichment is the technology itself.
HTTP Header Enrichment is the process of adding data fields in the HTTP header. When used in mobile networks in order to authenticate the mobile phone user, data that specify user and device identifiers such as IMEI, IMSI or MSISDN are usually added. HTTP header is readable by humans, it’s a simple textual protocol, not encrypted in any way so it can carry very sensitive and private data like users’ phone numbers.
Obviously, there is a huge security and data privacy issue when using header enrichment based 2FA. It looks like that within this technology, security is even more compromised in order to increase the user experience and, potentially user adoption. This definitely indicates that header enrichment as a mobile authentication option is not designed to fill the security gaps of SMS (or any other security gaps) – they are perfect for user retention and conversion. If we prioritise security – header enrichment based authentication is a serious step back.
The real jeopardy brought by header enrichment based 2FA solutions has already been seen by major players like Apple and Google, announcing plans on banning any HTTP request made to their devices.
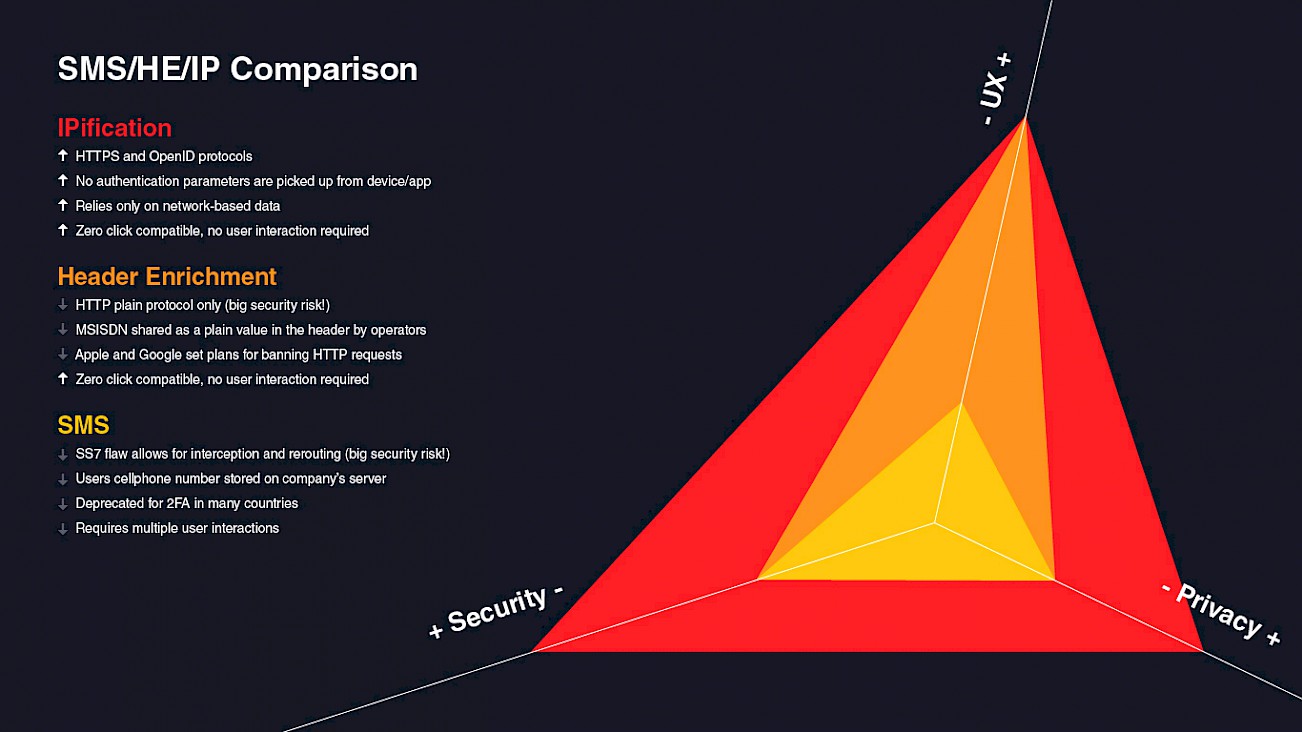
IPification – perfect user experience not compromising security
IPification is also using technology capabilities of mobile network operators globally but in a way that it is not making compromises between security, user experience, and privacy.IPification generates Unique Mobile ID including different data from Mobile Network. Thanks to this algorithm it is also possible to smoothly detect any SIM card and device related changes
When using IPification, the entire authentication process on a mobile phone is done automatically, within a fraction of a second without the need for any action performed by the user. This means that the process is as smooth as HTTP header enrichment but without any security risks.
IPification is in this sense a perfect method of mobile user authentication as it is capable to respond to every single challenge other telco-based authentication options have like SMS OTPs and HTTP header enrichment.
As long as security features rely on humans, our behavior or our personal information, authentication options will not be secure enough. Second – as long as the authentication method uses communication channels like SMS, messaging, email and HTTP, it will be possible to steal someone’s identity in so many ways.
This is why we need a totally different way of protecting our digital IDs. Solutions that will not rely on human behavior and will not require any user interaction whatsoever. A solution that will not use any bit of personal information like email, name, phone number, fingerprint nor will be dependent on insecure communication channels. This is where IPification comes in perfectly.